Although the term WiFi Mule is currently not part of the NIST glossary of terms, it is a technique that security teams should be aware of. During a cyber incursion, Incident Response teams will follow a standard set of playbooks: wipe computer systems, disable accounts & reset passwords, block malicious IPs and close firewall holes just to name a few. These steps are done to make sure the adversary is locked out and digital backdoors are closed. But what if the backdoor is sitting in an unsuspecting car in the parking lot?
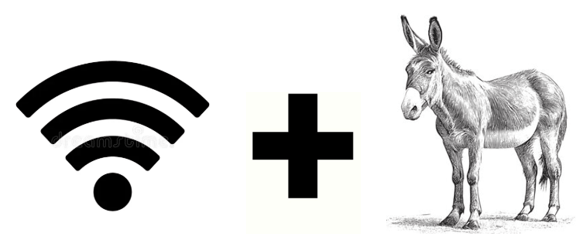
What is a WiFi Mule?
A WiFi Mule can be either a human or device used by a foreign Advanced Persistent Threat actor to help maintain persistence through a “physical bridge” into a compromised network. While the primary attack my be thousands of miles away, the Mule acts as a local wireless proxy. Usually with a cellular enabled laptop, that sits within range of the target’s WiFi network.
How the Tactic Works?
After the compromise, the APT will use the WiFi network credentials or may even add a hidden or spoofed ssid. Then the hired Mule is instructed to sit at a specific location at a specific time. Companies normally shutdown access to the external networks during their remediation process but will forget to perform physical sweeps and in many cases, leave local WiFi enabled. The APT will use the Mule‘s cellular connection to tunnel back into the network, bypassing newly hardened firewalls, to silently watch and relaunch another attack when the time is right.
Why it’s so effective
There are several reasons why this technique is effective. First, there is plausible deniability on the part of the ignorant Mule that helps to facilitate the attack. They may think they are only doing a WiFi survey. Second, there are no geoblocking alerts since the cellular IP is local and blends in with the WiFi network. Lastly, most organizations are focused on the cloud and don’t disable local WiFi or rotate WPA3 keys, which leaves a window open for the Mule.
Closing the Physical Loop
If the company is compromised by a sophisticated actor, IR playbooks must include physical site surveys that go beyond the walls of the building. These scans should look for rogue access points as well as unauthorized RF signals. Also, password/key rotation and zero-trust for any WiFi network needs to be included within corporate cybersecurity policies, as well as include this type of threat or other physical variations within routine TTX.
In the age of global APTs, the Mule sitting just outside the front door should not be forgotten.







